Managed Services
Next generation technologies, processes, and people for your IT strategy
Synergy Advisors provides best in class, end-to-end, proactive and reactive IT operation services, leveraging M365, Azure, and Synergy Advisors solutions across several scenarios:
Solutions covered by our managed services
(mouse over each image to see our services)
Secure E-mail
- Users
- Apps
- Services
- Hygiene
- Threats
- Data leak mitigation
Secure Collaboration
- Users (internal / external)
- Apps
- Services
- Hygiene
- Threats
- Data leak mitigation
Device Protection
- Application security
- O.S. security
- Security baseline
- Threats
- Data leak mitigation
Information Protection and Compliance
- Data in use
- Data at rest
- Data in transit
- Application integration
- Data leak mitigation
- Structured and unstructured data protection
- Information governance
Platform Protection
- Monitoring / services analysis / alerts and notifications
- Security baseline
Threat Protection
- Users (internal / external)
- Devices
- Identities
- Endpoints
- Cloud
- Monitoring
- Infrastructure
- Security baseline
Options according to your organization's needs
CORE
PREMIUM
CORE
Core Infrastructure
Cloud [IaaS / PaaS] and on-premises core infrastructure management
Security and Compliance
Protection, detection, and response for cybersecurity services for hybrid resources management
PREMIUM
Analytics
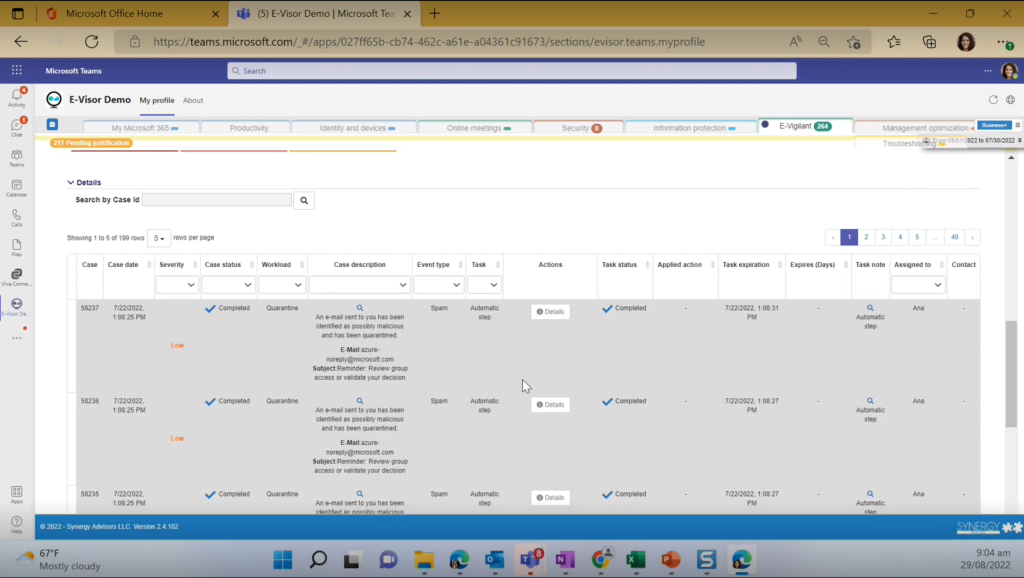
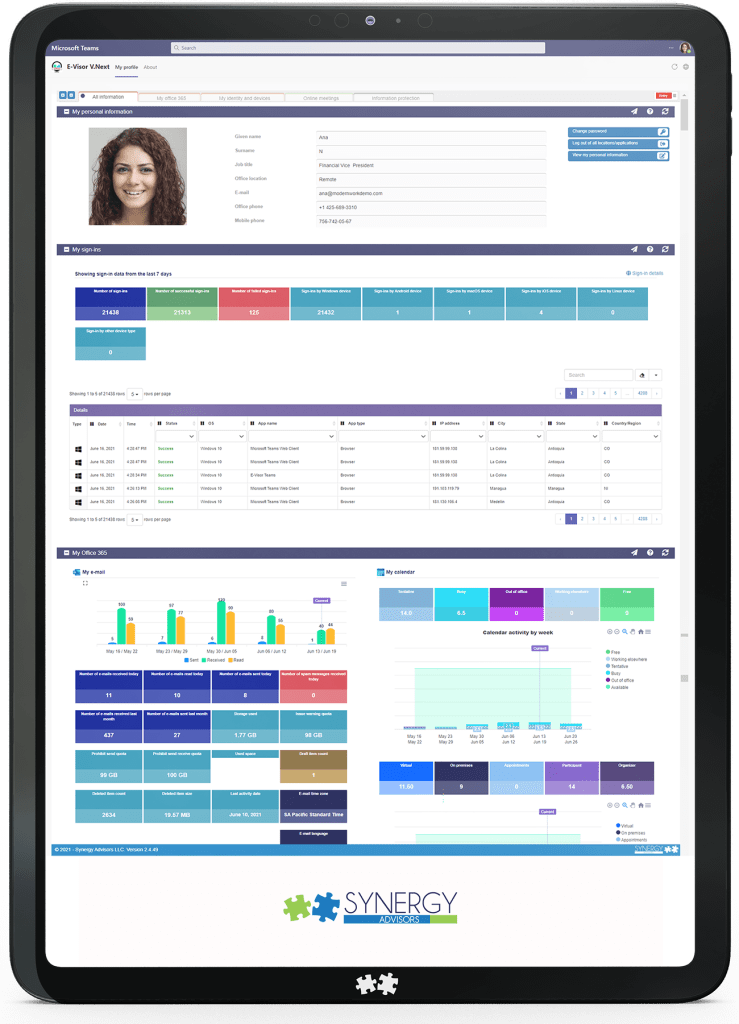
End-to-end cloud productivity and security resources analytics for adoption, security, and compliance visibility
Alerts and Notifications
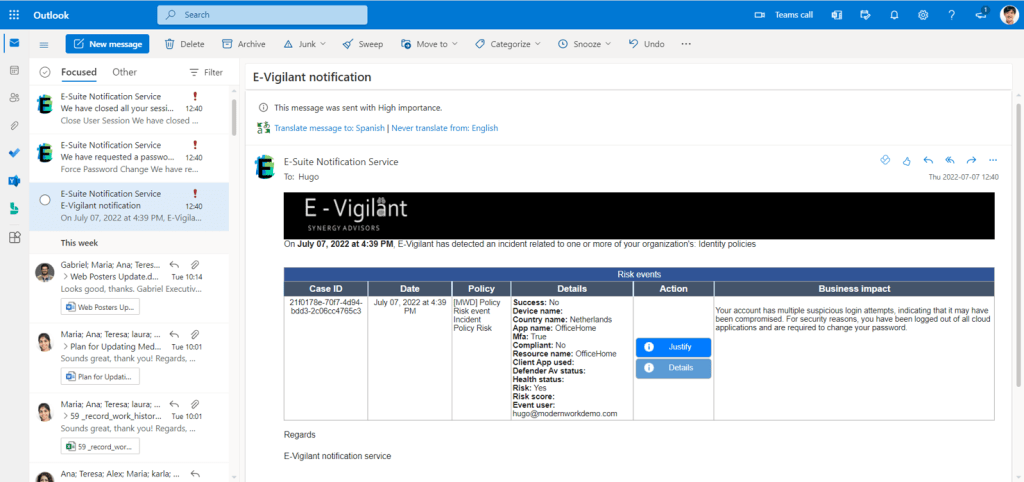
Optimized alerts management via workflow-based BOT notifications
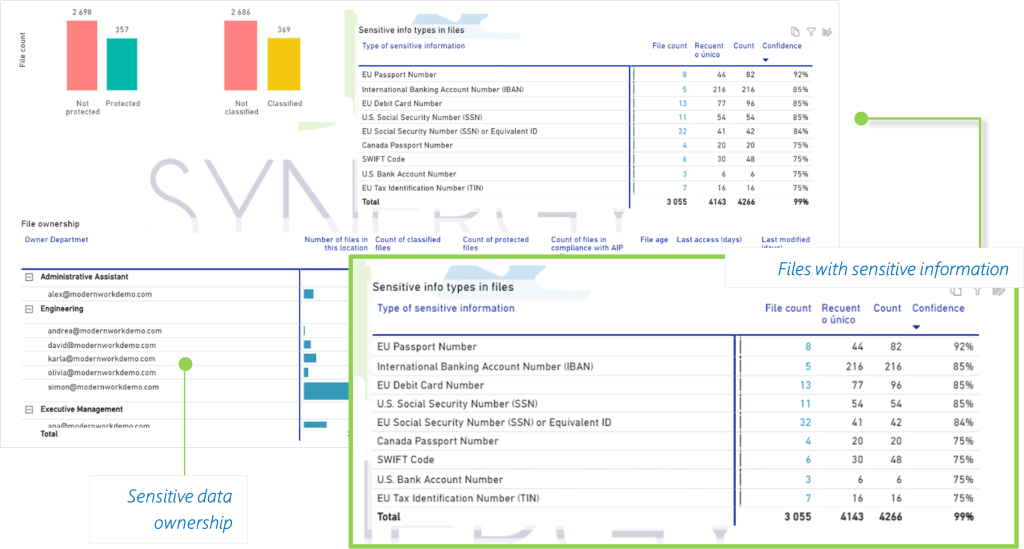
Advanced Data Governance
End-to-end information lifecycle management for unstructured data in use, data at rest, and data in motion
- B2B
- Compliance focused
End-to-end analytics and collaboration from Premium subscription
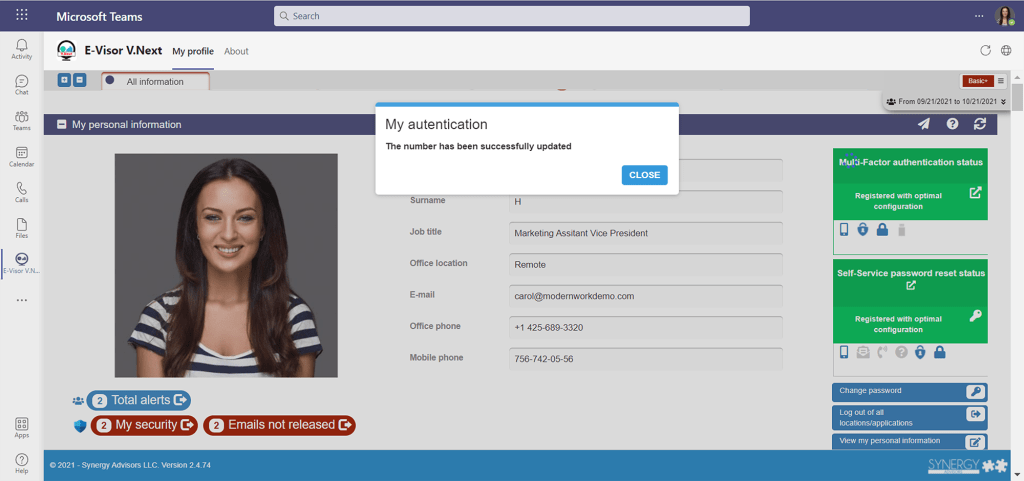
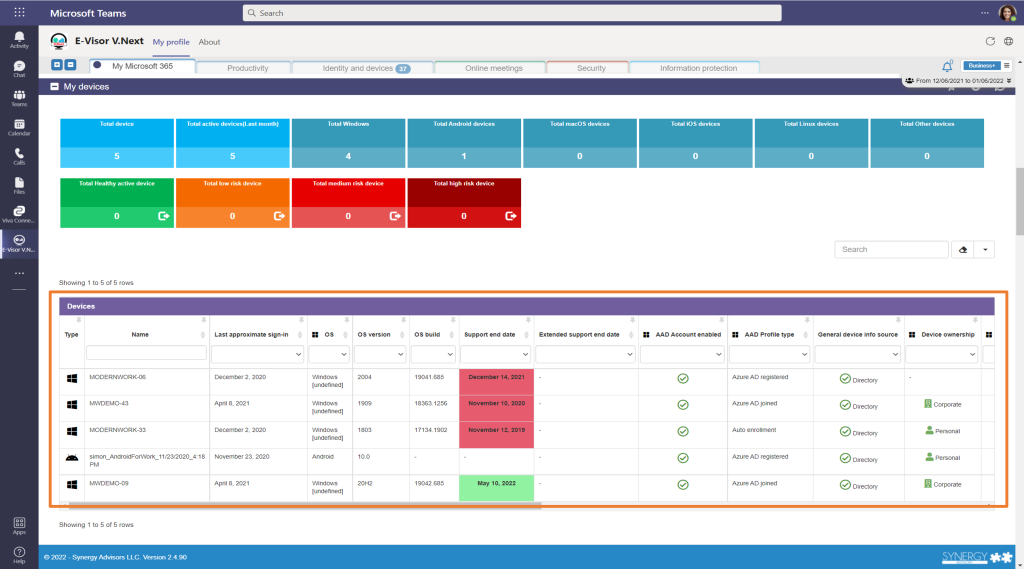
- Complete view of identities, devices, applications, and cloud information in a single dashboard
- Personal and team account status and information
- Sign-in status, risk events, and failed logins
- Identity and devices health and compliance status
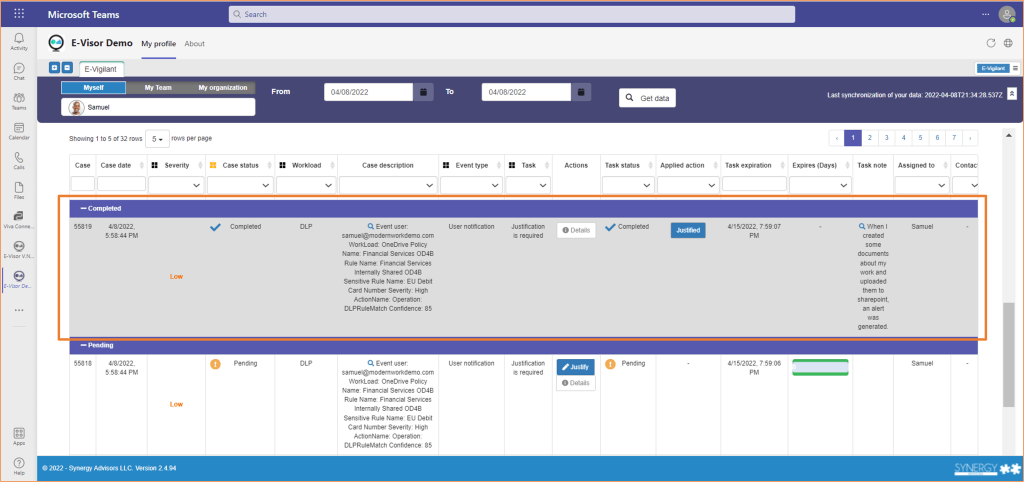
- Risk and security alerts and notifications
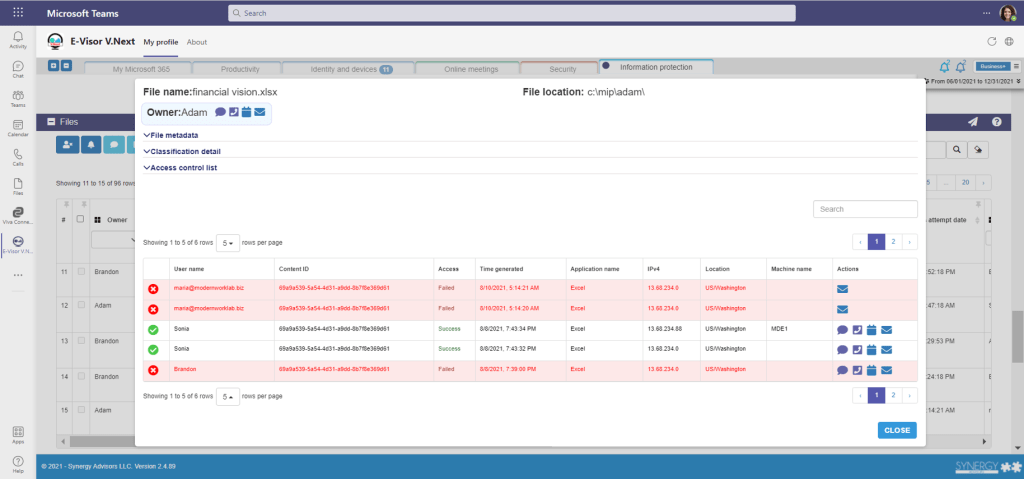
- Information protection policies
- Document lifecycle management and governance
- Sensitive data inspection and protection
- Alerts on security incidents, malware, and threats
Benefits
- IT time and cost reduction
- Better and more effective incident management
- Greater efficiency in risk mitigation
- Simplified and automated management
- Process optimization through analytics and reporting
- Faster response to security threats
- Involvement of the entire organization in cybersecurity management
- Increased effectiveness in technological processes
Managed services activities
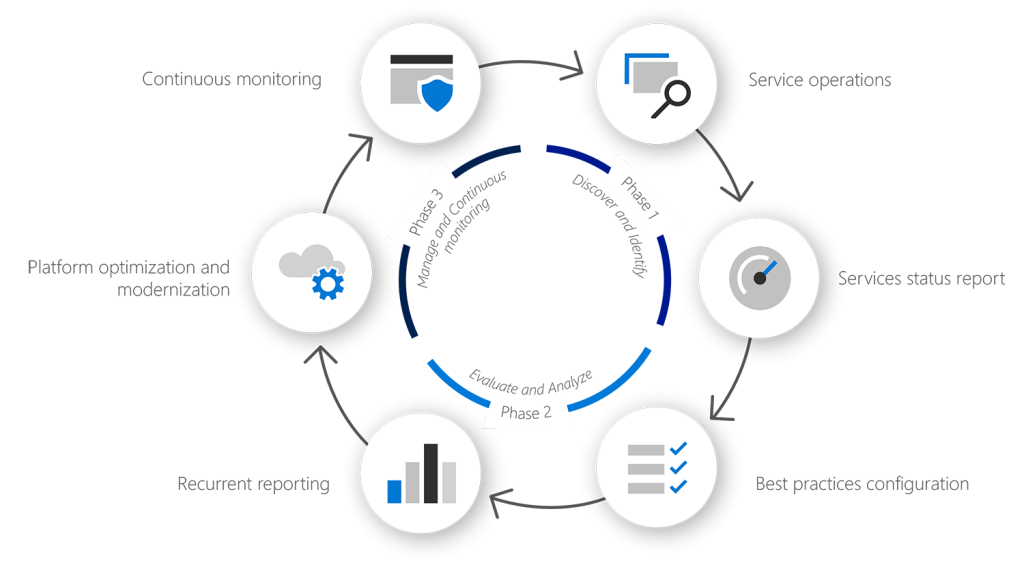
Service Operations & Incident Management

©2020 Synergy Advisors LLC. ALL RIGHTS RESERVED.
Contact Us at (+1) 425-689-3310 or through our Support Page