
Detect log4j vulnerabilities and help protect your organization with the E-Visor Teams App

The log4j vulnerability has impacted users worldwide and cybersecurity experts say the worst is still to come.
First, in response to the questions we’ve been asked, none of the Synergy Advisors solutions are affected by the log4j vulnerability.
Second, our E-Visor Teams App can detect if this vulnerability is affecting your infrastructure and help your organization heighten security against this, and other, threats.
What is the log4j vulnerability?
It’s a vulnerability that affects the open-source component log4, which is designed specifically for the Java programming language. It’s become somewhat of a standard for developers to use to simplify troubleshooting, auditing, and data tracking.
Even major companies, including Apple, Google, and Amazon, run this software. Potentially hundreds of millions of devices from around the world could be exposed to the vulnerability through popular apps and websites.
E-Visor Teams App and log4j
Protect Identities
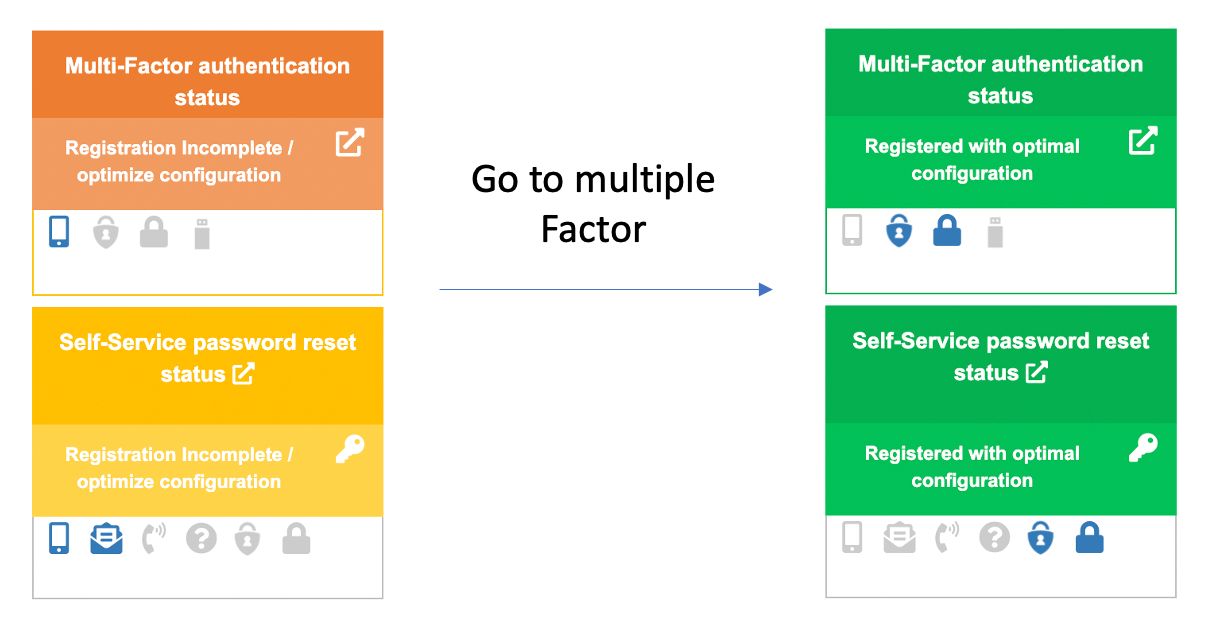
One of the most important actions an organization can take is to protect user identities. You can help empower users to check their enrollment in Microsoft identity protection tools with the E-Visor Teams App. From the My personal information section, users can review their Multi-Factor Authentication (MFA) and Self-Service Password Reset (SSPR) statuses to ensure they are enrolled and configured according to best practices.
More information about MFA and SSPR in the E-Visor Teams App
Protect Information
If your E-Visor Teams App license includes information protection capabilities, end users can review access attempts to their most sensitive documents and they can proactively respond to anomalous access attempts. Your users have the context necessary to help identify abnormal behavior; leverage their perspective to heighten your security posture and give them the tools they need to react.
More about Information Protection in the E-Visor Teams App
E-Visor Teams App log4j notification
The E-Visor Teams App can notify end users and administrators in the event that the vulnerability is detected in your infrastructure. Proactively, you can use the My security tab of the app to review your security status and respond to events, if necessary.
Other useful information
1.Know which technologies affected. This list shows the devices and services known to be affected and their current patch status, published by CISA: log4shell/software at main · NCSC-NL/log4shell · GitHub
2.Microsoft has published guidance for detecting and remediating Log4j2 risks in on-prem and cloud SaaS environments: Microsoft’s Response to CVE-2021-44228 Apache Log4j 2 – Microsoft Security Response Center
3.Extra help. Leverage our Security specialists who have been trained to address weaknesses such as the current log4j vulnerability. Contact us at [email protected] for more information.
Need more help? [email protected]


