
Passwordless: Elimination of passwords
Passwords are no longer the most secure and effective method to protect access to our systems. Passwordless is today the more effective way to secure identities and accesses:

 Windows Hello gives users a personal, secured experience where the device is authenticated based on their presence. Users can log in with a look or a touch, with no need for a password. Windows Hello leverages biometric authentication through fingerprints or facial recognition and is more secure, more personal, and more convenient.
User friendly and privacy protecting
Windows Hello gives users a personal, secured experience where the device is authenticated based on their presence. Users can log in with a look or a touch, with no need for a password. Windows Hello leverages biometric authentication through fingerprints or facial recognition and is more secure, more personal, and more convenient.
User friendly and privacy protecting
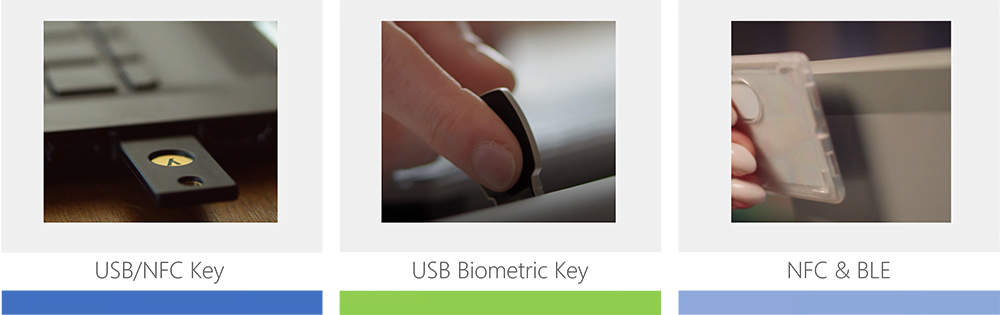
FIDO2-compliant security keys are cryptographic credentials in a variety of form factors, including USB keys or NFC-enabled smartcards. They can be protected with a second factor such as a fingerprint (integrated into the security key) or a device PIN to be entered at sign in.
 Microsoft Authenticator is a free mobile app on iOS and Android that can replace or augment passwords with push notification approvals, one-time passcodes, and additional verification of a biometric gesture on the device or the device PIN.
Microsoft Authenticator is a free mobile app on iOS and Android that can replace or augment passwords with push notification approvals, one-time passcodes, and additional verification of a biometric gesture on the device or the device PIN.

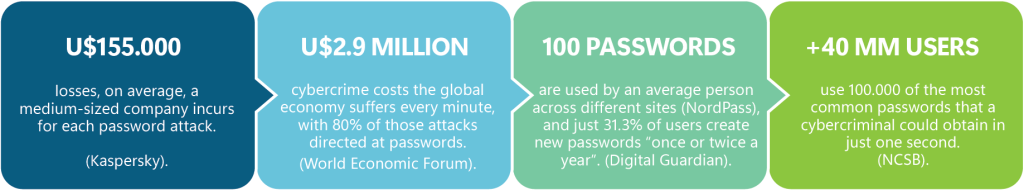
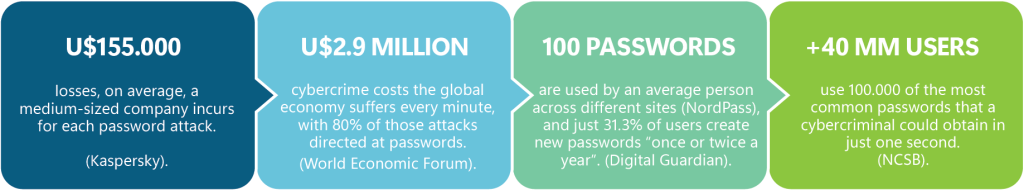
The problem
Passwords are expensive and vulnerable to breaches
- Password reuse across multiple accounts: 63% of workers admit to reuse passwords
- Passwords are the weak link: 80% of breaches leveraged passwords
- Data breaches are expensive: $3.86 million, the average cost of a data breach
- Passwords generate tons of support calls: 30-50% of help desk callas are related to passwords resets
Attacks and security breaches derived from the misuse of passwords
- Guessing
- Replay
- Phishing
- Brute force
- Password spraying
- Man-in-the-middle
- Key-logger
The solution: Move on to Passwordless
What is Passwordless Authentication
Passwordless is a disruptive authentication method in which a user can log in to a computer system, service, or application without entering (and having to remember) a password or any other knowledge-based secret.
Passwordless overview
- Something you have [Windows 10 Device, Phone, Security Key] + Something you are [Biometric] or know [PIN]
- Authentication based on Public/Private Keys pair
- Private Key are securely stored on the Device [PCs, Mobile Application, FIDO2 Key]
- Private keys are tied to a device and are never shared
- Requires the use of local gesture [PIN, Biometrics] to unlock the private key
Passwordless solutions
Windows Hello for Business
 Windows Hello gives users a personal, secured experience where the device is authenticated based on their presence. Users can log in with a look or a touch, with no need for a password. Windows Hello leverages biometric authentication through fingerprints or facial recognition and is more secure, more personal, and more convenient.
User friendly and privacy protecting
Windows Hello gives users a personal, secured experience where the device is authenticated based on their presence. Users can log in with a look or a touch, with no need for a password. Windows Hello leverages biometric authentication through fingerprints or facial recognition and is more secure, more personal, and more convenient.
User friendly and privacy protecting
- Passwordless: uses biometric authentication or a PIN
- Single Sign-on with Windows apps
- Biometrics data never leave the device
- Strong two-factor authentication
- Asymmetric key pair authentication model
- Can be deployed in cloud, hybrid, or on-premises environments
- Key or certificate-based options
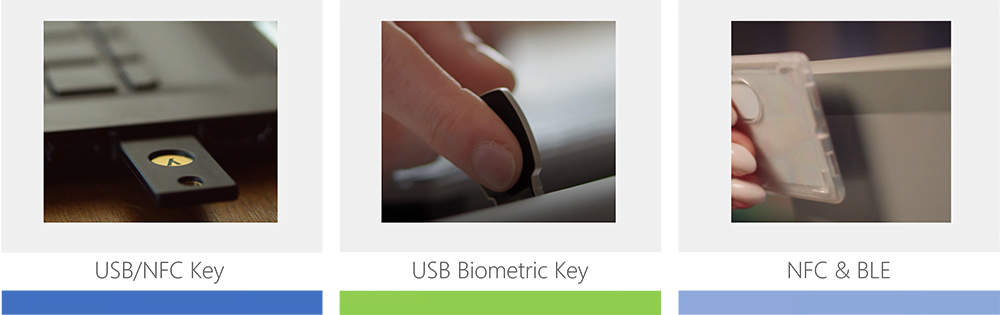
FIDO2 Secure Keys
- Authentication based on Hardware [Portable]
- Security devices that are Microsoft compatible
- Sign in using FIDO2 [biometrics, PIN, and NFC]
- Recommended for shared PCs scenarios or when a mobile device is not a viable option [Examples: help desk personnel, public kiosk, hospital team, bank teller]
- Recommended for Privileged and Critical Identities: Azure AD Global Administrator, Security Administrators, CEO, CISO, others
- Cross platform if using as Smart Card [on-premises services required]
Different options according to your organization’ specific scenario
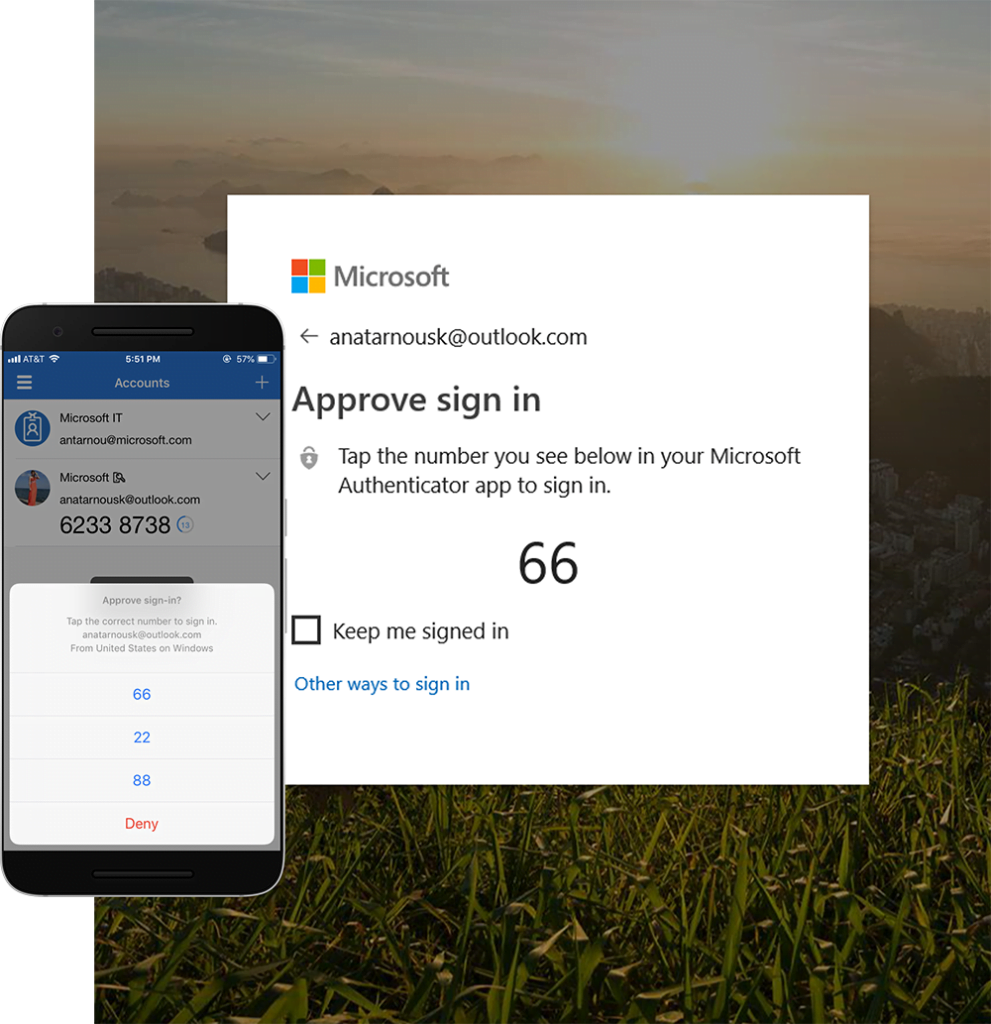
Microsoft Authenticator
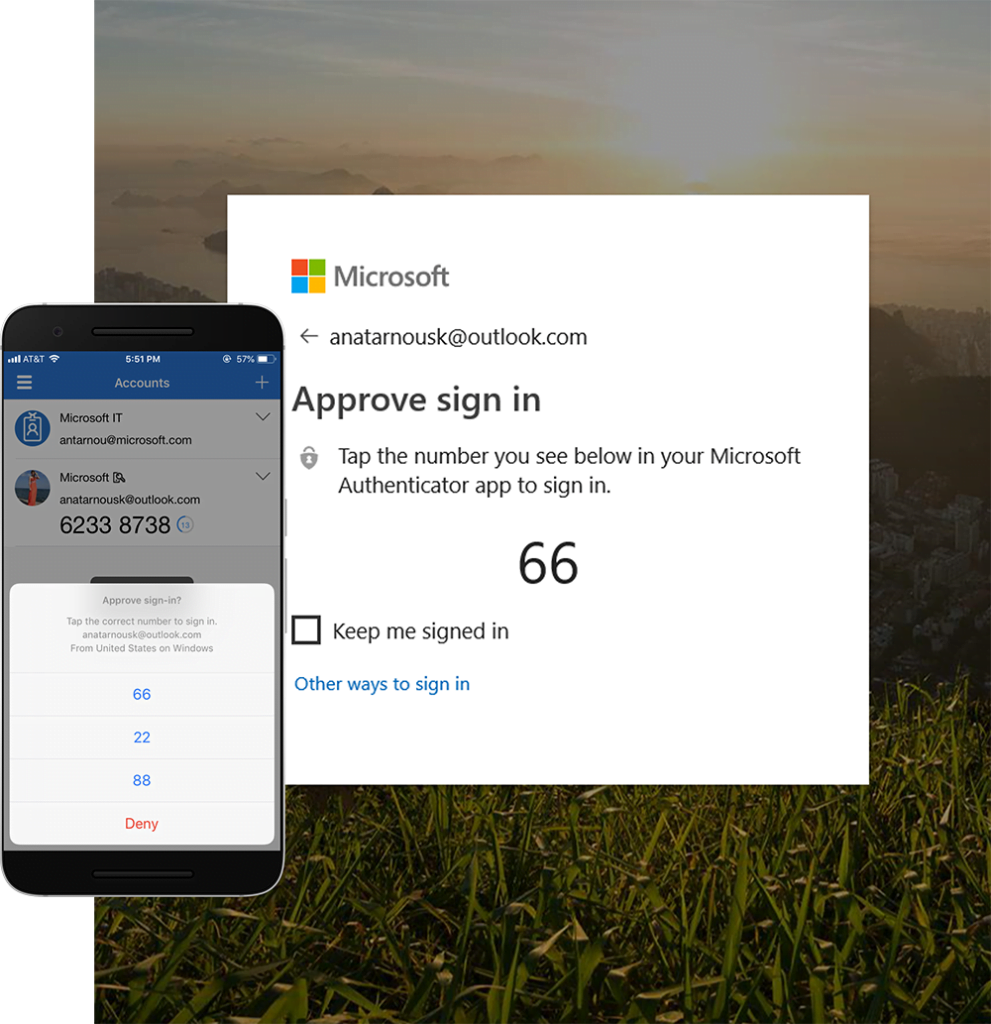 Microsoft Authenticator is a free mobile app on iOS and Android that can replace or augment passwords with push notification approvals, one-time passcodes, and additional verification of a biometric gesture on the device or the device PIN.
Microsoft Authenticator is a free mobile app on iOS and Android that can replace or augment passwords with push notification approvals, one-time passcodes, and additional verification of a biometric gesture on the device or the device PIN.
- Authentication based on Software
- Standards based MFA
- Supports TOTP, Push Approvals, Biometrics + Number Match
- Sign in using a mobile device with fingerprint scan, facial or iris recognition, or PIN
- Applicable for accessing work or personal applications on the web from any device.
- Users can sign in to any platform or browser by getting a notification to their phone, matching a number displayed on the screen to the one on their phone, and then using their biometric (touch or face) or PIN to confirm
Extended identity capabilities with E-Visor Teams App
E-Visor Teams App complements the passwordless strategy by presenting to end users, managers, and IT department the MFA configuration status, sign-in information filtered by risk events, failed logins, location, devices, identity and much more, as well as self-protect actions.Simplified end user Multi-factor Authentication and Self-Service Password Request (SSPR) management
- Reduce complexity to access Microsoft 365 information spread along with multiple sites, reducing costs
- Reduce user education as Microsoft portal adds/removes information/capabilities and changes URLs
- Simplified user experience providing multiple technologies/workloads view with the same look and feel
- Reduce time and create awareness
- Mitigate phishing attacks
- Reduce troubleshooting and support time
- Self-service
- Reduce organization cost
- Empower end users to strengthen their security posture
How to take the most from Passwordless technologies?
Introducing E-Suite Offerings [E*O]
Synergy Advisors offers you the way to enhance your identity governance strategy through the E-Suite Offerings (E*O): activities performed in your tenant that use Microsoft and Synergy Advisors technologies and enable you to proactively discover anomalies, remediate gaps, protect information and resources, and monitor your tenant activity:
The best E*O for your Passwordless strategy
- E-Suite DISCOVERY Offering [EDO]: One-week assessment to enable and validate MFA existing configuration, while validating conditional access rules, and discover identity and access-related gaps.
- E-Suite REMEDIATION Offering [ERO]: Remediate MFA adoption and optimize conditional access rules, to remediate gaps detected at the EDO phase.
- E-Suite PROTECTION Offering [EPO]: Remediation for all impacted users (in previous E-O) using chatbot technology.
